Introduction
If you're in the information security industry, or plans you may have to find all available information security certification. Back, I started really no use, there is no degree, no professional information security certification. It was only some high-level from SANS, then more things such as security + and CEH have follow-up.
Respect for the industry, I found the certificate as the GIAC SANS recognition and Cisco CCIE's just pure understanding of the network also go through. Some people walked through the main purpose is to interest management in the CISSP, and the Iron and Steel Association .
In recent years a number of technical and more convenient courses and certificate have been appearing, such as Opst (I think) and OSCP program . The oldest section of CEH 3 has been considered to be a script Keady certificate, while it is still like this - even though it greatly over the years it still should not be what (I had taught three sections of CEH) to improve.
In any case, the problem is, there is a new kid on the block - from the recently launched eLearnSecurity known as penetration testing - Pro (PTP) to use the "slogan" What CEH three paragraphs should be.
Knowledge of the course itself contains 3, 4 more than 1600 hours of video and interactive communication in the field learning laboratory slides. It is a Japanese guy for a long time I know Armando Romeo hackers center with Brett and the famous pair of four United Nations Development Nitin & Vipin Kumar. If you've been reading about in the dark for a long time most likely you have read here about Nitin and Vipin said, we VBootkit around the Waters signature.
The course also has an optional certification requirements for certification of professional penetration tester (eCPPT) should be the most relevant courses in 0-3 years of experience between the objectives. It covers all the basics of the approach to achieve the advanced technology, especially in the system security in part by Nitin and Vipin wrote.
The course
Program itself is basically a penetration testing program , covering three main areas of system security, network security and network application security. It almost covers the behavior you need to know, as penetration testing every 3 theme is quite common. Course supplies also made itself does not limit its order, you can learn the subject, there is no linear progression, so you can pick and choose depending on your mood.
Let us look at the sub-section.
System Security
In the system security topics are as follows:
- Module 1: Introduction
- Module 2: cryptography and password cracking
- Module 3: Buffer Overflow
- Module 4: Shellcoding
- Module 5: malicious software
- Unit 6: Rootkit coding
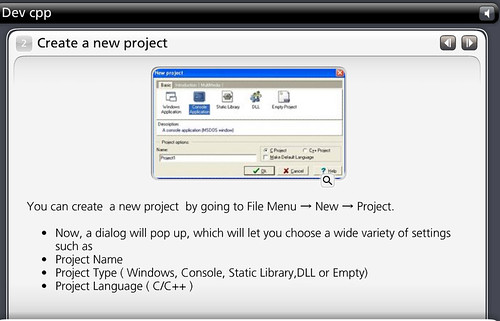
You will fare much better, if you Zai这个topics such as some coding of Jing Yan, because it is a fairly deep head start Jin Xing Kai Fa, C + + Zhong using assembly language and NASM's . This may be the most intensive part of the curriculum, particularly at sea.Implementation of this course once again I wrote 2 years back, that is - you need to learn Assembly (ASM) of .
This is why I say that programming will help, they do not have a spoon to eat the ASM and C + +, so you need to do some work themselves. However, if you already have some knowledge of two languages, you will have certain advantages. They also include the Windows driver development knowledge base.
Since then, it is the harder stuff on, each covering a wide range of topics, but there are enough pointers so that you can continue to do more research yourself. When it comes to cryptography, the same subject, you can spend four years just to do one - so do not expect to become a master overnight. Remember the focus of this course is to become a professional penetration testing, so you must know enough to do your work.Although almost all the bases covered here, such as encryption module alone has around 150 slides (some of which contain sub-slide), so that the budget for this for quite some time.
The shortest part of the Rootkit module, but then how much you can write rootkit? As long as you understand the concept and how they work, you usually are good to go.
Network Security
- Module 1: Information gathering
- Module 2: scanning and detection of target
- Module 3: Count and footprint
- Module 4: sniffing and MITM attacks
- Module 5: Virginia and exploitation
- Unit 6: Anonymous
Network security may subject I like, when you get into a deeper message Anquan you Huiqingxiangyu Zhaodao some of the things you are You have affinity, Ye Xu natural Ren Caizai these areas or simply more interest. Either way, for me, this has been the network security.
It follows you with a pen test (information gathering, scanning, enumeration quite logical structure / fingerprints on the attack, and then). They explore the many tools, but also noted that many in there, it can not cover all - plus they really brief tool. Use familiar / tools are you proficient, but it is easy to find them - just look at Google, of course, we have good tools, the stock of a network hacker dark here.
Because such a tool of Nmap and Maltego very well.
Vulnerability assessment and development part (the fun part!) Covered by Nessus's and Metasploit good. There are quite a few films in this section, which makes the whole thing more interactive. The film tends to adopt a voice in the form of a screen cam.
Web Application Security
- Module 1: Introduction
- Module 2: Information gathering
- Module 3: Vulnerability Assessment
- Module 4: XSS attack
- Module 5: SQL injection attacks
- Module 6: Advanced Web Attack
Web application security is of course the latest and most popular topic right now and security has in the past few years, more and more important data moving online, e-commerce and online payment solutions sites, it's a critical area.
The two main things you need to know in the Web application security is the XSS (cross site scripting) and SQL injection .
The code sample is mainly based around PHP is justified, the content is well structured from the beginning (database structure) has been advanced SQL injection attacks began. I personally think this is the most powerful in the courseware, and one of the most useful part, for the creation of these modules props Armando.
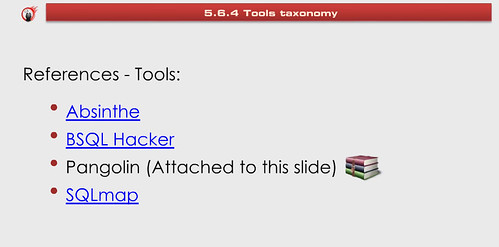
He also gives a good low-down tools, the most popular SQL injection, and even what features are supported by each classification. If possible, the tools associated with, in some cases directly connected to the instant download of slides.
Appendix
- Methods: The process information
- Methods: Form
- Report: Guide
A main difference with this course, not only teach you how to 'hack' and left it there - the course also includes a specialized information on how to deal with, and how to create report part.
As a professional penetration teser (and most), I personally hate the part of the report ... but if you want to get paid this is a necessary evil. You should know that the report clear, concise and methods for your discovery. This is a very important part, in a realistic, Virginia / Wednesday the project could actually be accounted for 30-50% of the time the report in total, this is a safe bet in most cases, if the work will be time-consuming 2 weeks report will take another 1-2 weeks of the most important.
Laboratory
The laboratory's a customized version of the back four composed of building Web applications in a fragile, there is a laboratory on how to set up a comprehensive PDF Download eCPPT certification.
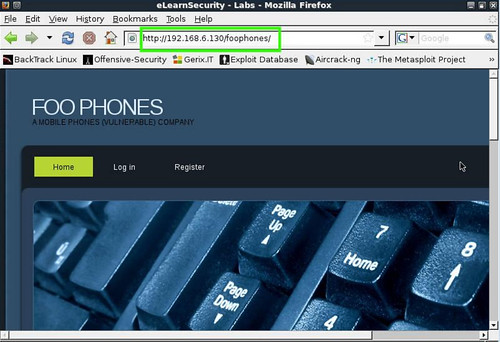
If you really working hard to complete the actual assessment should not be a big problem. The certification exam is a virtual laboratory, and over the report's comprehensive and careful valuation will be one of our instructors produce practical pentest - there's not much choice or automatic marking here. Do you really want to prove that you know you've learned - including the report part.
Conclusion
In general in my opinion, if you are looking penetration testing training, this is a great choice, even if you do not want to take the registration You can learn Henduo just applying Ziji by a major research of the modules and. Perhaps if the new information security (1-2 years), do you think you have some weak links, or blind spots you can fill these with the class.
If you are just starting (still in research or new graduates) I think the course and certification will be certainly be a positive impact on your career. Only $ 599USD it is the cheaper products on the market one, of course, is in the economic comparison, to their real life to participate in 5 days of the course. Of course, it also gives you time to consider your strengths, and make sure you really understand each module - more different here [PDF format].
It into a lot more than three paragraphs as CEH course depth and can really benefit from your skills. I hope such a thing in 1999 when I started. In which the materials, the proposed approach is more interactive and interesting than many other courses, a good combination of text, images and video with a good theory / practice mix in there. This makes it very easy for the theme of many of the internal information security can be very dry very quickly.
You can view the complete course outline: syllabus.pdf
If you have any more questions, you can check frequently asked questions here PTP .

Hey Nice Blog!! Thanks For Sharing!!!Wonderful blog & good post.Its really helpful for me, waiting for a more new post. Keep Blogging!
ReplyDeletedot net course training in coimbatore
IT security training in coimbatore
This comment has been removed by the author.
ReplyDeleteI found This Content worth reading. I am regular reader. I want add that if any students want expert training or placement assistance for advanced penetration testing certification course
ReplyDelete